Zero-day vulnerabilities are flaws or weaknesses in software or an operating system of which the developer or vendor is unaware. Hackers discover these vulnerabilities first, giving developers and vendors “zero days” to release a patch. Zero-day vulnerabilities can cause not only immediate headaches for developers and vendors but also long-term impacts on a business posture, customer trust and loyalty, and even national security.
The use of more advanced technologies, and speed in experimenting and innovating, including artificial intelligence may mean that zero-day vulnerabilities will soon become increasingly common.
Here is a list of cases with consequences and complications of zero-day vulnerabilities, made up by 17 members of Forbes Technology Council. This is the information organizations need to know and leverage now to better protect themselves.
- Months May Pass Before A Vulnerability Is Discovered
Our company is in the insurance industry, and our policyholders’ data and our intellectual property are our most important assets. Zero-day vulnerabilities directly impact both. The exposure date and the discovery date are two different things, and months can pass before a vulnerability is discovered. Limiting exposure to the outside world, subnetting your networks, and limiting user privileges will help mitigate this issue. — Francisco Diazluna, Producers National
- They Can Grant Backdoor Access To Systems
If left untreated, zero-day vulnerabilities can lead to exploits, backdoor access, and unsecured channels or even disrupt operations. For protection, businesses must increase visibility to identify any blind spots associated with zero days and develop rapid workarounds. Humans must become aware of zero-day operations and their nature and implement self-protection standards and awareness controls. — Dewayne Hart, SEMAIS
- They Can Lead To Financial Losses
Zero-day vulnerabilities can cause financial loss and damage to a business’ reputation. The exploitation of these vulnerabilities can potentially lead to the theft of sensitive information and the disruption of critical operations. Prioritize proactive measures: Assess vulnerabilities, including citizen-developed apps deployed with open-source and low-code/no-code apps, and deploy continuous monitoring to ensure compliance with policies. — Diane Robinette, Incisive Software Corporation
- Customers May Lose Trust In A Business’ Systems
The biggest long-term consequence of zero-day and other vulnerabilities is that people lose trust in the company’s systems. Aside from using best-in-class security software and establishing strong policies, I think network segmentation is a great approach. When you divide your network into many segments, attackers can’t access the whole network by accessing one part, and this limits the potential damage. — Marc Rutzen, HelloData.ai
- They May Enable Cyber Warfare
One possible long-term effect of zero-day vulnerabilities is that they can be used as weapons by government-sponsored groups or other bad actors to carry out spying or cyber warfare. These attacks can have serious consequences, such as disrupting important infrastructure, stealing sensitive data from governments or businesses, or even causing physical harm. Use security software and multifactor authentication. — Mohamed Fathy, EFG Hermes
- Legacy Tools May Miss ‘Unknown Unknowns’
Zero-day exploits continue to grow, accelerated by a nation-state focus and tools including ChatGPT. These “unknown unknowns” can avoid detection for months due to the failure of legacy tools that rely on signatures. Needed protection comes from tools with predictive generative abilities that automatically learn each environment to provide real-time detection of suspicious activity that deviates from the expected. — Matt Shea, MixMode
- Defenders Are Forced To Be Reactionary
For cybersecurity programs focused on predicting the attack vector, zero days are true “unknown unknowns” that force these types of defenders to be reactionary and give attackers the advantage. Businesses should develop security programs that use an understanding of “normal” behaviors to detect and disrupt any anomalous activity and autonomously enforce what’s “normal,” ensuring operational resilience. — Marcus Fowler, Darktrace
- Attackers May Lie Dormant In A System
The biggest consequence is that attackers can get into a system immediately, before a patch is ready, and lie dormant. This is why a proactive approach is so important: You need to know where your vulnerable devices are and implement zero-trust segmentation. This means communications are limited to only what is needed to function, reducing the attack surface and minimizing lateral movement. — Jim Hyman, Ordr
- Cyberattacks Could Increase In Frequency And Severity
One potential long-term consequence of zero-day vulnerabilities is an increase in the frequency, impact, and severity of cyberattacks. To protect against this threat, businesses and individuals should adopt proactive security measures such as keeping software and systems up to date, using strong passwords and two-factor authentication, implementing network segmentation, and conducting regular security audits and assessments. — Favour Femi-Oyewole, Access Bank PLC
- Humans Will Need To Remain As Part Of The Cybersecurity Equation
The existence of zero-day vulnerabilities ensures that in the long term, humans will not be removed from the cybersecurity workplace equation. When AI systems are given fundamental flaws in coding, they read that as the anticipated output of the code, and as such cannot flag certain software behaviors as flaws. This dynamic ensures the fundamental and ongoing need for humans within cybersecurity. — Dara Warn, INE
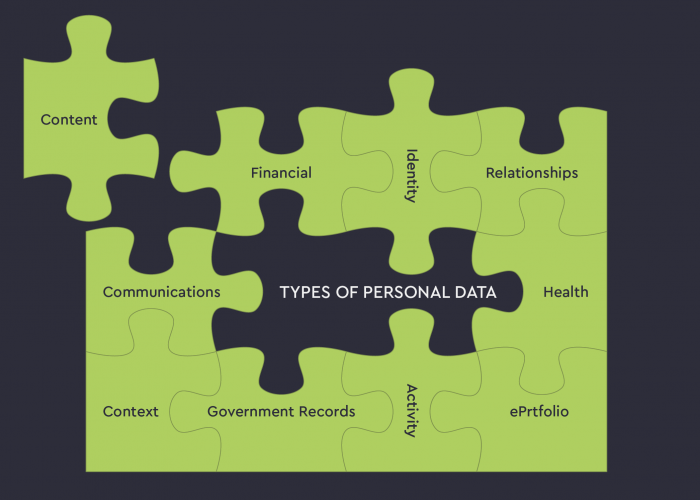
- They Can Lead To Data Exfiltration
Zero-day vulnerabilities can allow attackers to take control of systems in order to compromise them, which can eventually lead to data exfiltration. Proper access controls to limit access to systems, applications, and data to only authorized users can reduce the impact of the vulnerability, even if it is exploited. — Zechariah Akinpelu, Unity Bank PLC
- User Privacy And Data Integrity May Be Compromised
The existence of zero-day vulnerabilities can result in severe consequences, including widespread breaches that can compromise user privacy and data integrity. You can lessen this risk by keeping software up-to-date by regularly patching it, requiring multifactor authentication, using robust security protocols, and increasing cybersecurity awareness among employees and users, both in business and personal settings. — Brian Greenberg, Fortium Partners LP
- Detection And Response Windows May Shrink To Hours Or Even Minutes
Zero-day vulnerabilities are here to stay, and threat actors will become increasingly more aggressive, meaning security organizations’ detection and response window will shrink to hours or minutes. In the long term, organizations will need to fast-track zero-trust and AI-first strategies to combat zero-day threats and develop a comprehensive threat intelligence mechanism to understand the vulnerabilities impacting their ecosystems. — Raj Utraja, Gore Mutual Insurance
- There Could Be An Increase In Successful Cyberattacks
As zero-day vulnerabilities become more prevalent and easier to exploit, cybercriminals will be motivated to launch more frequent and sophisticated attacks. This could result in a significant increase in the number of successful cyberattacks and the damage they cause—all of which will likely be exacerbated by the emergence of new technologies such as ChatGPT. — Eyal Benishti, IRONSCALES
- Public Trust In Critical Infrastructure May Be Eroded
Attacks enabled by zero-day vulnerabilities erode public trust in critical infrastructure, necessitating proactive defense-in-depth measures and robust incident response. Information-sharing and collaboration via channels such as MS-ISAC and fusion centers are crucial for rapid response to advanced persistent threats and threats posed by nation-states. This can strengthen cybersecurity efforts, restore confidence, and preserve national security. — Mia Millette, Skyline Technology Solutions
- They Necessitate A Layered Defense Strategy
Zero-day attacks come from both state-sponsored actors and individual hackers, making it challenging to protect businesses because of the limited ability to detect and prevent them. Companies must adopt a layered defense strategy that includes an awareness campaign, obsolescence strategy, zero-day assessments, segmentation, detection and prevention, and proactive vulnerability research and reverse engineering. — Mike Walker, Microsoft
- They Can Be Traded In The Exploits Market
Zero-day vulnerabilities can go unaddressed for months, giving hackers—not just one hacking group, but multiple groups—immense opportunities to exploit them. This fuels hacking groups to harvest and trade more zero days in the exploits market. Eventually, we’ll see increased motivation for researchers to share their findings in the black market instead of reporting them to vendors. — Aviv Grafi, Votiro
Source: Forbes