Any CISO will tell you one of the biggest issues they face is insider threats — particularly in large organizations where sensitive data is plentiful and easy to take.
With the growing number of cyberattacks and data breaches, businesses are swiftly approaching more robust security mechanisms. And zero trust architecture is one of them.
Don’t trust anything, because if we trust nothing, we’re more likely to prevent bad things from happening.
Zero trust can be defined as the security concept based on a belief that enterprises shouldn’t automatically trust any device or individual, whether inside or outside its perimeters and should strictly verify everything before granting access.
In a nutshell, zero trust relies on the principle of “don’t trust anyone.” This architecture cuts all access points until proper verification and trust are established. No access is provided until the system verifies the individual or device demanding access to the IP address, instrument, or storage.
This strategic initiative helps prevent data breaches as the concept of trusting anyone is eliminated, even if the access request is from within the network. Hence, implementing zero trust architecture ensures the highest level of security and mitigates the risk of a data breach or unauthorized access.
Implementing a zero-trust architecture in today’s era is crucial since cybercriminals are exploring new ways of breaching organizations’ security. Moreover, in a post-covid world, where remote working has swiftly become the new routine, identity thefts and unauthorized access are creating big hurdles for enterprises.
Hence, it’s crucial for organizations to think outside the box and not just rely on conventional security mechanisms, including multi-factor authentication. Zero trust architecture has become the new normal.
But how can enterprise security architects go from that broad, overriding philosophy to a workable, adequate protection against insider and other threats?
- Identity:
Employees must use enterprise-managed identities to access the applications they use in their work. Phishing-resistant MFA protects those employees from sophisticated online attacks.
To ensure properly controlled privileged data access, enterprises must employ risk-based access by taking a holistic view of users and gaining a deep understanding of their responsibilities and authorities, as well as having the ability to verify user identities when they attempt to access data. They must also implement strong enterprise-wide authentication practices and consolidate the means of authenticating to as few department-managed identity authentication systems as practicable. This improves insights into “normal” user activities, enables better detection of abnormal behavior, facilitates more effective security policies that limit unnecessary access, and enables quick detection and action against anomalous behavior.
- Devices:
Enterprises must maintain a complete inventory of every device it operates and authorizes for business use so they can prevent, detect, and respond to security incidents on those devices.
- Networks:
Enterprises must encrypt all DNS requests and HTTP traffic within their environment, and begin executing a plan to break down their perimeters into isolated environments.
- Applications and Workloads:
Departments within enterprises must treat all applications as internet-connected, routinely subject their applications to rigorous empirical testing, and welcome external vulnerability reports.
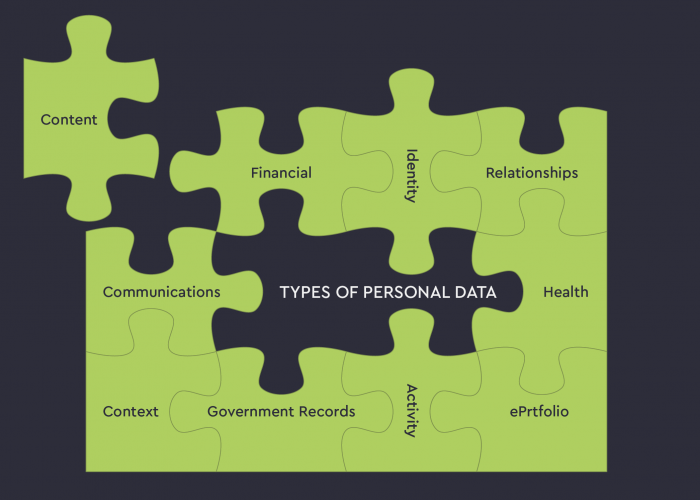
- Data:
Create a clear, shared path to deploy protections that make use of thorough data categorization and security responses, focusing on tagging and managing access to sensitive structured, unstructured, and semi-structured documents.
Enterprises should leverage whatever cloud security services are available to monitor access to their sensitive data, and implement solutions that enable enterprise-wide data visibility, logging, and information sharing.
The road to a zero trust model is long and rarely aligned with the traditional cybersecurity strategies to which we have grown accustomed. The good news is, the more goals you can achieve that lead to a real zero trust model, the better you will be at mitigating security risks to your enterprise