Are you curious about what 2021 is going to bring us in terms of cybersecurity? Of course, everybody hopes for the better, but in fact year to year the situation is only getting worse. While we were busy with COVID-19, cybercriminals were looking for new effective ways to make money. According to ZDNet, they succeeded once again. We are talking about cyber extortion and new tactics used by hackers.
Who is the target?
One of the large companies recently affected by the Clop ransomware told ZDNet that criminals used a new approach in a cyber attack. Now their target is not ordinary employees, but the working devices of top managers. Why is that?
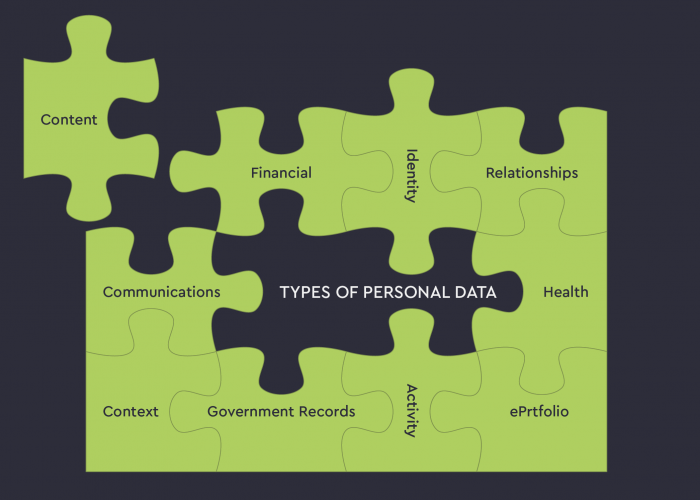
There are two reasons. First, chief executives are exactly those who make the decision to pay the ransom out. Second, such devices may contain personal information that can be used to put pressure on the victim.
According to media reports, finally, the company paid a multimillion-dollar ransom. ZDNet contacted other victims of the Clop ransomware and found out that the same tactic was used in all cases.
The evolution of ransomware groups is evident: from random attacks on ordinary users to targeted attacks on large corporations. Such «gangs» penetrate into the corporate network, steal confidential files, encrypt them, and leave their digital notes on the devices` screens with specific requirements and the description of consequences in case of refusal to pay the ransom. They have the only goal – to get money using powerful psychological pressure.
Each hacker group hopes that the company affected by the ransomware will try in every possible way to prevent data leakage. It’s not just reputation, money, and possible information leakage to competitors at stake. Companies are also afraid of heavy penalties for the breach.
How is it going?
Hackers are combing through the files and emails of top managers to get information that can be useful to put pressure on decision-makers regarding ransom payout.
A bad practice
ZDNet says similar tactics have become popular among other ransomware attackers, for example, REvil (Ransomware-as-a-Service) is already using the same approach. Not surprising, because if the new way of putting pressure maximizes the chances to get money, why not to take the advantage of it?
Experts say that often hackers don’t really own the data, but simply bluff and play on our fears. In the case of top executives, the number of pressure methods is on increase, because people really have something to lose: a position or even worse – a reputation gained over the years.