Verizon’s annual Data Breach Investigations Report (DBIR), conducted since 2008, finds that modern data breaches can be almost entirely connected with a combination of employee mistakes and supply chain compromises; one of these elements will almost certainly be involved in any organizational cyber incident.
82% of data breaches logged in 2021 involved a “human element” such as:
— falling for phishing,
— re-use of stolen credentials,
— insider malfeasance or simply causing a configuration error.
61% of breaches in 2021 involved a supply chain partner, something that criminals are increasingly targeting in an attempt to gain access to a variety of organizations at once.
Criminals prefer human fallibility to code flaws, ransomware continues to ramp up, overwhelming majority of incidents are financially motivated
There has been an alarming rise (13%) in ransomware breaches – a jump greater than the past 5 years combined, Verizon has revealed in its report.
Key findings
- 82% of analyzed breaches over the past year involved a human element (human error, misuse of privilege, social engineering attacks, etc.)
- External actors are 4 times more likely to cause breaches in an organization than internal ones
- Roughly 4 in 5 breaches can be attributed to organized crime
- “Financial gain” is the number one motive for the overwhelming majority of data breaches, “espionage” is in the second spot
- Over half of breaches involved the use of either remote access or web applications
- 62% of system intrusion incidents came through an organization’s partner (mostly due to single supply chain breaches)
- The vast majority of breaches include only a handful of steps, with three actions being most common (Phishing, Downloader, and Ransomware)
- 90% of the 5,212 data breaches analyzed could be put into one of these nine categories:
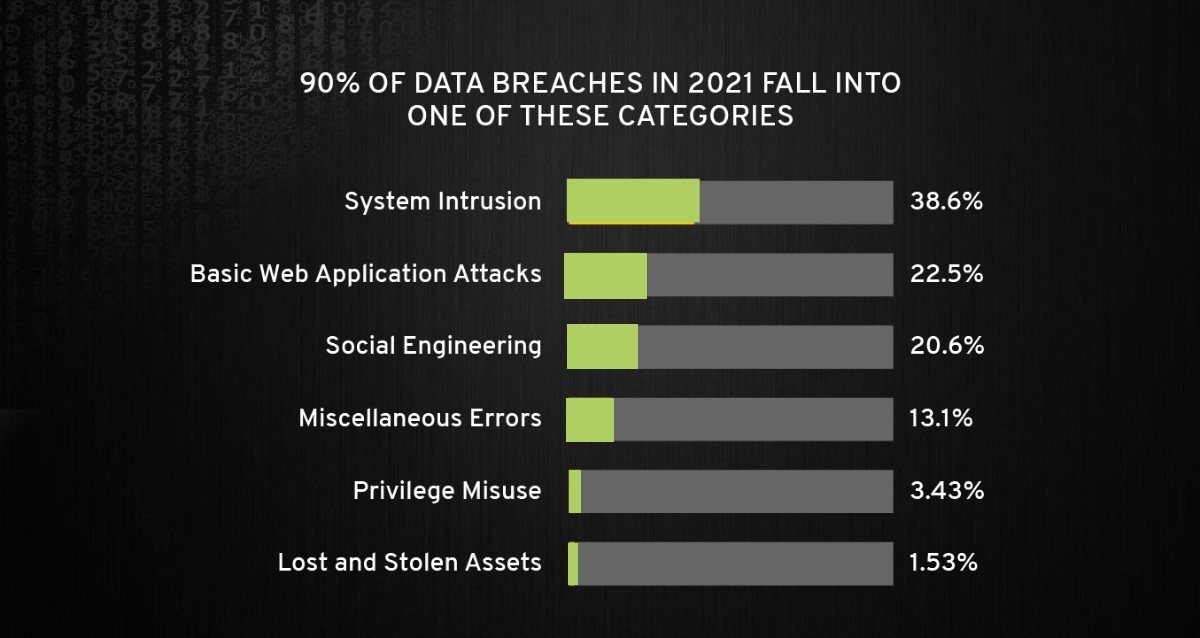
When all the analyzed incidents are taken into consideration, Denial of Service (39.7%) is the most prevalent category.
Figthing ransomware and preventing data breaches
40% of Ransomware incidents involve the use of Desktop sharing software and 35% involved the use of Email. There are a variety of different tools the threat actor can use once they are inside your network, but locking down your external-facing infrastructure, especially RDP and Emails, can go a long way toward protecting your organization against Ransomware.
Very small businesses – those employing 1 to 10 individuals – are also often targeted by ransomware gangs, and should worry about stolen credentials and social attacks (BEC scams in particular). The report includes advice on what to do to avoid becoming a target and what to do if you have become a victim.
As they pointed out, the four key paths to data breaches – including those due to ransomware – are credentials, phishing, vulnerability exploitation, and botnets, and no organization is safe without a plan to handle each of them.
Dave Hylender, Lead Author of the DBIR, says that while the report has evolved in these 15 years, the fundamentals of security remain the same: “Assess your exposure, mitigate your risk, and take appropriate action. As is often the case, getting the basics right is the single most important factor in determining success.”
Paul Laudanski, Head of Threat Intelligence at Tessian, says that while it’s staggering to see that 82% of breaches involved the human element, it’s not necessarily surprising.
“Generally speaking throughout the years, I’ve seen social engineering lead to a number of cyber incidents, from the execution of malware to phishing sites that collect credentials. It is not unlike those late-night infomercials, where people get caught in a moment that actors exploit. As humans, it’s in our nature to be helpful, but a good targeted social engineering attack will exploit this to compromise systems, breach data or withdraw funds. That’s why it’s so imperative to have solutions in place that go beyond rules and standard detections. Instead, tools must understand humans and our behaviors,..” he opined.
Source: Verizon