What’s the Difference Between a Data Leak and a Data Breach
The trend of global data breach events is steep and still continuing to tilt upwards. According to the latest data breach investigation report by IBM and the Ponemon Institute, data breach costs in 2021 have reached a record high. Last year, the average cost was US$3.83 million, and this year it has peaked at US$4.24 million.
Mitigating these events involves comprehensive management of the entire attack surface, including the third, and even fourth-party vendor network.
While the proliferation of cybercrime is forcing organizations to improve their cybersecurity programs, many are still overlooking one of the primary causes of data breaches – data leaks.
To learn the common causes of these critical security events, and how to mitigate data breaches by addressing them, read on.
What is a Data Leak?
A data leak is an overlooked exposure of sensitive data. These exposures could occur physically – like a post-it note containing login information – or, more commonly, electronically – through software vulnerabilities.
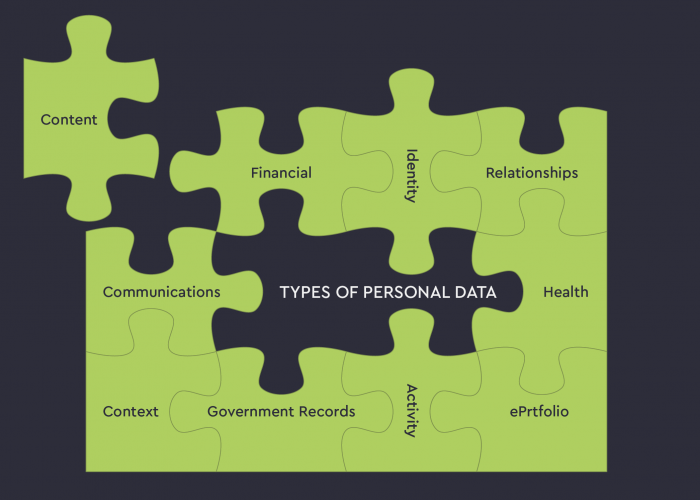
When cybercriminals discover data leaks, they could use the information to launch a successful cyberattack – especially if the exposed data contains Personal Identifiable Information (PII).
What’s the Difference Between a Data Leak and a Data Breach
Data leaks are not initiated by cybercriminals. They fall through overlooked vulnerabilities and remain unknowingly exposed to the public. These exposures could remain for years before they’re eventually discovered by either cybercriminals or security teams.
Data breaches, on the other hand, are entirely caused by cybercriminals. They are the intended objectives of planned cyberattacks.
Data leaks are usually caused by internal errors
A data breach is the intended outcome of a planned cyberattack
Though they have different origins, both data leaks and data breaches could result in the compromise of sensitive data. Data leaks usually occur before data breaches and provide cybercriminals with the necessary ammunition to make cyberattacks happen much faster.
But not all data leaks develop into data breaches. Some events could facilitate the deployment of ransomware attacks (which could be classified as data breaches).
The 6 Most Common Causes of Data Leaks in 2022
1. Misconfigured Software Settings
Misconfigured software settings could expose sensitive customer records. If the leaking software is popular, millions of users could then be exposed to potential cyberattacks.
This was the cause of the Microsoft Power Apps data leak in 2021.
2. Social Engineering
Data leaks are rarely initiated by cybercriminals, but when they are, it’s usually a result of tactical trickery through social engineering.
Social engineering is the use of psychological manipulation in order to garnish sensitive credentials from victims. Phishing is the most common type of social engineering attack, occurring either verbally or electronically.
An example of a verbal phishing scam is a threat actor calling an employee while impersonating an IT technician. The threat actor could request login credentials under the pretence of reinforcing access in response to a critical internal issue.
Experian suffered a data breach impacting 800,000 businesses from a verbal social engineering attack. A cybercriminal posing as one of Experian’s clients requested services from the company, which eventually resulted in the release of sensitive customer data.
Hackers could then use the data leak to breach an IT perimeter and complete the initial phase of a cyberattack sequence.
Electronic phishing attacks are more proliferative since they can reach a larger list of victims much faster. The most popular form of social engineering is email phishing.
Phishing emails pose as legitimate communications from reliable sources, but their contents contain infected links. When a user clicks on a phishing email link, they could either initiate the clandestine installation of malware or load a dummy web page designed to steal data.
Phishing emails are becoming increasingly sophisticated and harder to detect, especially when they take advantage of recipient anxieties.
A sudden increase of such immoral practices shadowed the COVID-19 pandemic. Phishing emails detailing fake safety information were sent to victims, some even claiming to be from government agencies and popular healthcare entities.
3. Recycled Passwords
In many cases, a single compromised password leads to the compromise of multiple digital solutions because users tend to use the same password across all of their logins.
This poor security practice creates a critical data leak because stolen customer data is usually sold via dark web forums.
You can check whether your emails, passwords, or phone numbers were compromised in historical data breaches by visiting Have I Been Pwned.
If you’re an iPhone user, iOS 14’s Security Recommendations feature enables you to check if you’re reusing passwords so you can change them immediately.
Even partial password information is categorized as a data leak because the remaining portion could be uncovered through brute force methods.
During a brute force attack, multiple username and password combinations are attempted with automation tools until a match is achieved.
Having partial password information decreases the number of required attempts, helping cybercriminals achieve success much faster.
4. Physical Theft of Sensitive Devices
Company devices contain sensitive information, and when these devices fall into the wrong hands, they can be leveraged to facilitate security breaches, or identity theft, leading to data breaches.
For example, a cybercriminal could contact the IT administrator from a stolen laptop and claim that they’ve forgotten their login information. With the right persuasive tactics, the IT administrator will divulge this information, helping the cybercriminal remotely log into the company’s private network.
5. Software Vulnerabilities
Software vulnerabilities, like zero-day exploits, create convenient pathways into sensitive resources. This circumvents the initial stage of the cyberattack lifecycle, propelling criminals through to the privilege escalation phase of an attack lifecycle – the only remaining stage before a data breach.
6. Use of Default Passwords
Many of the factory-standard login credentials that accompany new devices are publically known, even to cybercriminals. Because of this, unchanged factory-standard credentials are classified as data leaks.
IoT devices are most impacted by such exposures. When purchased, these devices come with standard login combinations to support rapid setup.
Common username and password combinations include «admin» or «12345.»
Manufacturer instructions usually include a bold warning to change these credentials prior to use, but, unfortunately, they are seldom followed – a bad habit of both small businesses and large enterprises.
Because IoT devices are usually networked together, these data leaks could facilitate a large-scale DDoS attack.
This is exactly what happened in 2016. One of the largest DDoS attacks ever documented was launched against the cybersecurity blog Kerbs on Security.
The botnet that executed the attack comprised of 380,000 IoT devices that were seamlessly hacked through their default passwords.
How Do I Prevent Data Leaks?
To prevent data leaks, cybersecurity programs must include a data protection strategy. Not only will this support user data security compliance with regulatory standards, such as the GDPR, it will also adjust incident response plans to include a data leak remediation strategy.
The following best practices could mitigate data leaks and the data breaches they make possible.
1. Simplify Access Permissions
This shouldn’t be confused with forsaking Privileged Access Management. Privileged access management is critical for cybersecurity, the workflow that manages the access levels of each user needs to be simplified.
Complex access permission workflows make it difficult to track each user’s access level, making it very easy to accidentally grant a user deeper access than they require.
Audit each user’s access levels to ensure that only those that absolutely require it have access to sensitive resources.
After this is complete, run your user access workflow through a very fine filter to eradicate unnecessary complexities.
2. Educate Staff
A data leak prevention strategy should include a primary focus on the most significant security threat to an organization – human error.
To prevent staff from falling for common social engineering tactics, they should be trained on how to accurately recognize when an attack is taking place.
The best form of training is experience. Establish a training program where staff are routinely targeted with controlled social engineering attacks delivered by your security team.
“Failing” a test creates a very impactful and teachable moment that will be remembered for many years.
3. Use Multi-Factor Authentication
Should an employee still fall for cybercriminal trickery after training, compromise could still be avoided with multi-factor authentication.
Multi-factor authentication creates an additional hurdle that could cause employees to rethink their actions during a social engineering attack.
4. Encrypt All Data
If data is accidentally leaked, it could have little use to cybercriminals if it is effectively encrypted.
Be sure to use the most secure forms of encryption such as AES encryption and PGP encryption.
5. Use a Password Manager
Default passwords are used because businesses have too many passwords to remember. A password manager conveniently stores all passwords in a single platform.
6. Implement a Data Leak Detection Solution
Each of the above strategies encourages best practices that could avoid data exposures, but they fail to detect the complex data leaks that might still fall through advanced security loopholes.
To tie off a data leak prevention strategy, best practices should be accompanied by a data leak detection solution.
Data leak detection solutions scan both the surface and the dark web to discover data leaks within cybercriminal interactions. These solutions can either be fully automated or supported by cybersecurity analysts.
Source: UpGuard