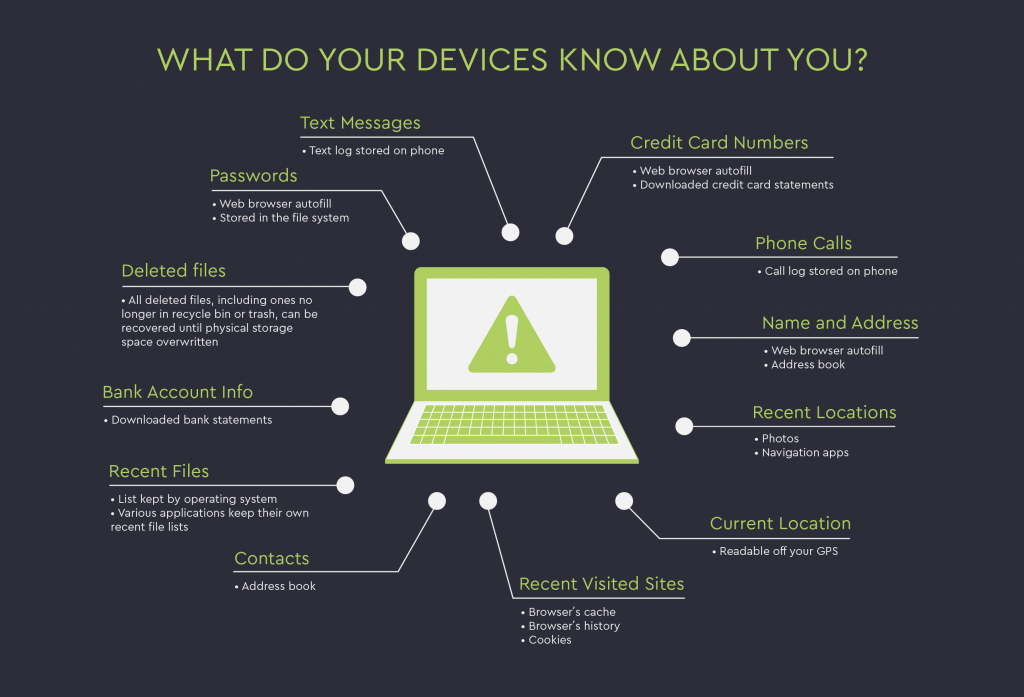
Passwords
- Web browser autofill
- Stored in the file system
Deleted files
- All deleted files, including ones no longer in recycle bin or trash, can be recovered until physical storage space overwritten
Bank Account Info
- Downloaded bank statements
Recent Files
- List kept by operating system
- Various applications keep their own recent file lists
Contacts
- Address book
Current Location
- Readable off your GPS
Recent Locations
- Photos
- Navigation apps
Recent Visited Sites
- Browser´s cache
- Browser´s history
- Cookies
Name and Address
- Web browser autofill
- Address book
Phone Calls
- Call log stored on phone
Text Messages
- Text log stored on phone
Credit Card Numbers
- Web browser autofill
- Downloaded credit card statements